Today, most organizations agree that cybersecurity risk is also a primary business risk. As organizations look for ways to reduce their cybersecurity risks while being mindful of their budgets, many are turning to multi-year plans to gradually increase the strength of their cybersecurity program. One of the best ways to organize and prioritize your cybersecurity planning is by using the NIST Cybersecurity Framework (NIST CSF). Let’s look at what is included in the NIST CSF and the business benefits of NIST Cybersecurity Framework implementation.
What is the NIST CSF?
The NIST CSF is the leading tool to help organizations manage cybersecurity risks using a framework of standards, guidelines, and practices. It is not compulsory; it is best practice. The NIST CSF serves as the underlying information security standard for many regulatory requirements and is a widely adopted, voluntary cybersecurity standard. Created as a strategic planning and assessment tool, it can help organizations of all sizes and all levels of cyber maturity understand and manage cybersecurity risk by using the framework to develop and organize security practices that build a strong cybersecurity posture in its six "Core” activity areas: Govern, Identify, Protect, Detect, Respond, and Recover.
 The primary benefits of NIST Cybersecurity Framework implementation are the ability for organizations to organize and prioritize cybersecurity risk reduction and create a multi-year improvement plan. However, since the NIST CSF was developed for a diverse group of organizations, it is not prescriptive to a specific business or industry. It is a framework that you need to interpret and apply based on your organization's specific cybersecurity risks. Let's look at the components of the NIST CSF so you can understand the benefits for your business.
The primary benefits of NIST Cybersecurity Framework implementation are the ability for organizations to organize and prioritize cybersecurity risk reduction and create a multi-year improvement plan. However, since the NIST CSF was developed for a diverse group of organizations, it is not prescriptive to a specific business or industry. It is a framework that you need to interpret and apply based on your organization's specific cybersecurity risks. Let's look at the components of the NIST CSF so you can understand the benefits for your business.
An Overview of the Components of the NIST CSF
The NIST CSF has three main components:
NIST CSF: Core
In simple terms, the Core includes six "Functions"—Govern, Identify, Protect, Detect, Respond, and Recover. The "Functions" are fairly comprehensive and cover topics including people, processes, and technology. It provides specific guidance on how to assess, organize, and match cybersecurity activities to outcomes (such as policy creation or added controls) in these six functions and their 23 categories listed in the following image:
As you can see, these functions cover the lifecycle of cybersecurity incidents and guide you to create plans for proactive risk reduction, incident detection, and post-incident response and recovery. Within each of the categories above, there are 108 Subcategories that dive into detailed action plans to drive business outcomes that are specific to your organization's needs. For example, in the identify function, you may need to create a cybersecurity inventory and asset management list that documents all connected equipment (laptops, phones, IoT and POS devices, etc.). It will then guide you to use this information to create a policy, procedures, and management processes that ensure equipment is maintained, upgraded, tracked, approved, and properly decommissioned. This is just one area of the CSF; this requires a deep dive into your organization's people, processes, and technology.
NIST CSF: Implementation Tiers
The NIST CSF implementation tiers are a way to categorize the level to which your organization has integrated cybersecurity risk management.
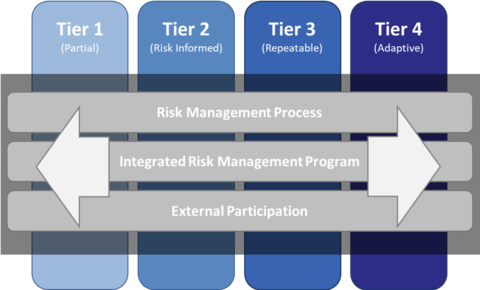 The tiers reflect a progression from reactive security programs to programs that are agile and risk-informed. The target tier for your business can vary by category, depending on your goals, risk tolerance, and budget. For example, you may decide to transfer some risks by purchasing cyber insurance and accept some low-priority risks based on budget constraints. These tiers help you document and organize this information, so you can use it to continuously increase your cyber maturity.
The tiers reflect a progression from reactive security programs to programs that are agile and risk-informed. The target tier for your business can vary by category, depending on your goals, risk tolerance, and budget. For example, you may decide to transfer some risks by purchasing cyber insurance and accept some low-priority risks based on budget constraints. These tiers help you document and organize this information, so you can use it to continuously increase your cyber maturity.
NIST CSF: Profile
This is a key tool to help your organization create a multi-year plan that prioritizes cybersecurity improvements in alignment with your organization's budget, risk appetite, and priorities. NIST CSF profiles help distill the information you gathered in the Core and Tier categories to organize and communicate your current status and goals, as well as identify and prioritize your long-term cybersecurity improvement. You can (and should) revisit it each year to update your cyber maturity growth and ensure that last year's decisions still align with your organization's goals, risk tolerance, and current cybersecurity threat trends.
The Business Benefits of NIST Cybersecurity Framework Implementation
The primary business benefits of NIST Cybersecurity Framework implementation are the deep assessment of your current cybersecurity posture and a long-term planning tool to prioritize and track cybersecurity improvements. With the ever-evolving cybersecurity landscape, threats evolve over time, and the NIST CSF is one of the best tools you can use to ensure your organization has an appropriate plan to counter today's threats and continue to strengthen your cybersecurity posture over time.
In addition, an increasing number of clients, regulators, partners, and cyber insurers are requiring organizations to provide proof of cybersecurity risk reduction technologies and plans. By using the NIST CSF, you will have gathered the information you need to communicate your continuous cybersecurity improvement plans and be able to prove your current efforts and future roadmap.
Operationalizing the NIST CSF Drives Down Business Risk
As great as the NIST CSF is, it is not without implementation challenges. While the flexibility of the NIST CSF enables any organization to use it as a strategic planning and assessment tool, the guidance is often ambiguous, and it can be difficult to understand how to apply the framework to your organization's unique environment. For organizations that find this process overwhelming, we developed the SE aCSF (Adaptive Cybersecurity Framework) that enables us to operationalize the NIST CSF for clients (and, in fact, go beyond the basic framework to incorporate additional best practices and expertise). SE aCSF enables us to:
- Operationalize the NIST CSF into our managed services to deliver long-range cyber maturity enhancements to our managed IT services clients.
- Provide professional guidance to help you adopt the NIST CSF as your information security framework, which includes a comprehensive aCSF Assessment.
For over 35 years, Systems Engineering has successfully navigated the evolving technology landscape providing small and medium-sized organizations with the right-sized IT services that enable them to move their businesses forward securely. Learn how Systems Engineering can do the same for you.
For more information on securing your organization using the SE aCSF, connect with us at info@systemsengineering.com or call 888.624.6737. Clients, please get in touch with your Systems Engineering Account Manager.
* Images used in this article are courtesy of the National Institute of Standards and Technology.







