Cybersecurity incidents are on the rise and not slowing down. This year, the nation has seen malicious cyberactivity against private sector companies such as SolarWinds, Microsoft Exchange, and most recently, the Colonial Pipeline. Cybercriminals also took advantage of the chaos brought on by the pandemic. The sudden work-from-home environments opened doors for new cyberattacks against small to medium-sized businesses (SMB).
According to the latest report from the data breach team at Verizon, what is changing is the level of sophistication and persistence of these cyberattacks. The aftermath of these incidents has caused widespread harm to the point that the Federal Government is responding. Here are some key findings from the latest Verizon Data Breach Investigations Report (DBIR), the top cybersecurity concerns for SMBs, and the steps needed to minimize those threats.

Executive Order on Improving the Nation’s Cybersecurity
This May, the White House signed an Executive Order (E.O.) to improve the nation's cybersecurity and protect federal government networks by recognizing that "incremental improvements will not give us the security we need; instead, (…) bold changes and significant investments (need to be made)…". The E.O. also states that cybersecurity requires more than government action since much of the critical infrastructure being attacked is owned and operated by the private sector.
Verizon 2021 Data Breach Investigations Report
 Malicious cyber activity was on the radar long before this governmental intervention. Since 2008, Verizon has published a data breach report each year from data compiled by both small businesses and large enterprises throughout the world to create the "Data Breach Investigations Report," or DBIR. Verizon creates this report to "increase awareness of where possible dangers lie, and how organizations may best avoid them." As all businesses realized last year, change can occur quickly and often without warning.
Malicious cyber activity was on the radar long before this governmental intervention. Since 2008, Verizon has published a data breach report each year from data compiled by both small businesses and large enterprises throughout the world to create the "Data Breach Investigations Report," or DBIR. Verizon creates this report to "increase awareness of where possible dangers lie, and how organizations may best avoid them." As all businesses realized last year, change can occur quickly and often without warning.
It is impossible to predict the future threats your company will face, but you can strategize for likely situations based on sound data like the DBIR.
We know you are busy running a company, so to help your organization prepare for what may come, we have identified key take-aways from this year’s report. We have also taken excerpts from the Executive Order that mirror suggestions given within the Verizon DBIR focusing on threats against small and medium-sized businesses (SMB).
|
Key Findings:
Invest in Security Awareness Training for Your Organization
According to Verizon, 85% of breaches involved the human element. This success rate demonstrates that threat actors prefer to target unsuspecting people to steal credentials, infect computers with malicious apps, and hold data for ransom. Your employees are a critical defense against these threats and need regular security awareness training to prevent breaches and social engineering. Don’t forget to test them frequently by simulating phishing attacks.
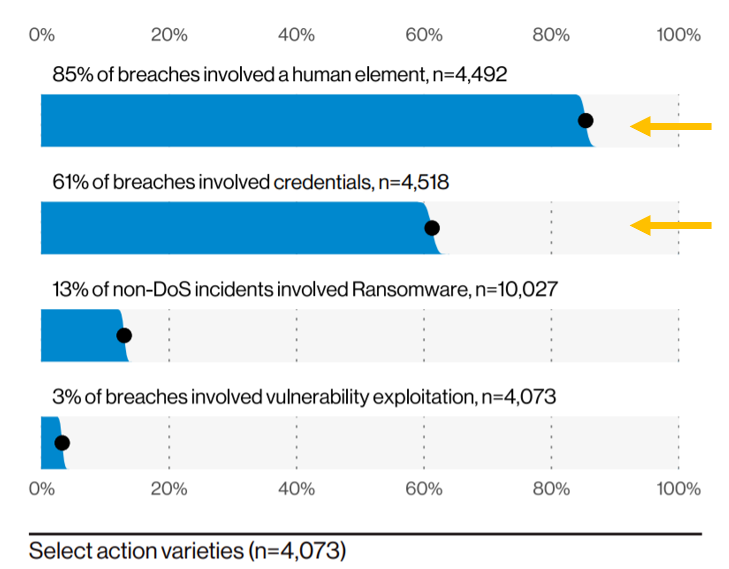
Implement and Enforce Multi-Factor Authentication
The use of stolen credentials is a favorite tactic of cybercriminals, with 61% of breaches reported involved credential data. One low-cost, proven security solution that prevents 99.9% of account compromise attacks is multi-factor authentication (MFA). This effective cybersecurity tactic is a multi-step authentication process that can reduce the chances of a cybercriminal successfully gaining access to your network, even with stolen credentials. In the Verizon report, U.S. Secret Service noted that organizations neglecting to implement MFA represented a large portion of victims targeted during the pandemic. As part of the E.O., Government agencies will begin to enforce the adoption of MFA and data encryption for data at rest and in transit by mid-November 2021 and consider MFA a foundational security tool.
Develop a Zero-Trust Architecture to Bolster Security Posture
The influence of the pandemic prompted many companies to adopt cloud computing at an accelerated pace to accommodate a seemingly overnight remote workforce, and cyber criminals took notice. Some organizations were not prepared for the need to care for the security and safety of client and corporate data living in cloud-based applications. Other agile organizations adjusted quite well. The difference was the implementation of a zero-trust security model. According to the DBIR, the U.S. Secret Service reported that a zero-trust model for (remote) access quickly became a fundamental security requirement (for organizations) rather than a future ideal. Having a zero-trust architecture proved to be a strong indicator of an organization's ability to prevent or recover from unauthorized presence in their network environment. The White House also noted such a compelling fact. The E.O. states that as Federal Government agencies continue to move toward cloud computing, they will move closer to a security model of zero-trust architecture.
Obtain Cyber Insurance for Your Organization
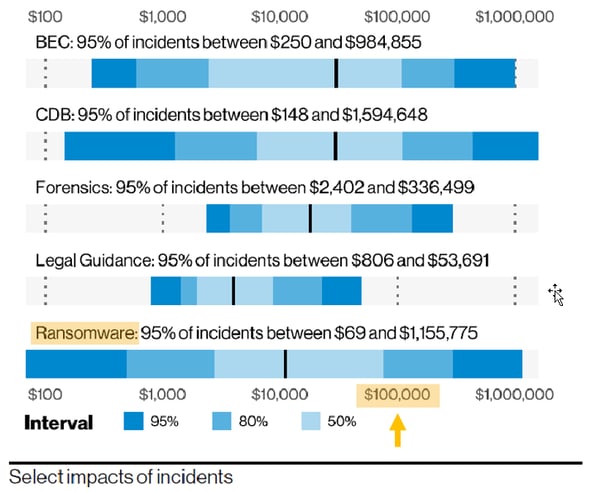
The increasing presence of ransomware (doubled from last year) causing breaches continues in an upward trend. More organizations fell victim to breaches last year, primarily from new tactics used by cybercriminals. In addition to stealing and encrypting data, cybercriminals are also publishing data to increase the likelihood that an organization will pay the ransom. By analyzing loss data, insurance costs data, and stock price data, the DBIR modeled the range of losses due to incidents. 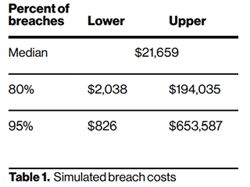 The median for incidents with an impact was $21,659, with 95% of incidents falling between $826 and $653,587. This statistic clearly indicates that organizations should obtain cyber insurance to transfer financial risk should a breach or significant security incident occur. This is not new advice but a reminder of how important it is to obtain coverage and be clear on what is covered and what is not. In the end, if you don't have breach insurance or don't qualify coverage, the DBIR statistics show that you should have $100k set aside "just in case."
The median for incidents with an impact was $21,659, with 95% of incidents falling between $826 and $653,587. This statistic clearly indicates that organizations should obtain cyber insurance to transfer financial risk should a breach or significant security incident occur. This is not new advice but a reminder of how important it is to obtain coverage and be clear on what is covered and what is not. In the end, if you don't have breach insurance or don't qualify coverage, the DBIR statistics show that you should have $100k set aside "just in case."
Every year, Verizon DBIR brings trustworthy statistics on where possible dangers lie and how organizations may best avoid them. This year, with the coinciding release of The White House E.O., it is apparent that cybercrime is at an all-time high. It is more important than ever to evaluate your organizational security posture and align your cybersecurity strategy with industry best practices. If you are not confident in the effectiveness of your cybersecurity controls and are looking for clear direction on where and how to fortify your organization against modern attacks, consider a quality cybersecurity risk assessment. Always remember that the best decisions are informed decisions.
If you are a Systems Engineering client and have questions about these Verizon key findings, please reach out to your Account Manager. Others, please connect with us at info@systemsengineering.com or call 888.624.6737.