Cyberattacks are on the rise. The Identity Theft Resource Center recently reported an annual all-time high in data compromises through the third quarter of this year1. The increase in cyber incidents means cybercriminals are sure to continue plaguing businesses well into the future. Consequently, cyber insurance coverage is now critical for small to medium-sized businesses (SMB) and is a key facet of any good defense strategy that prioritizes cyber resilience. Having this financial safety net in the event of a breach transfers a significant portion of the risk, ensuring you can cover the costs of recovery and remediation.
Cyber insurance is evolving, and requirements are changing. Over the past few years, we've witnessed a 3x growth rate, rate hikes, and re-underwriting. Even with stabilization, suppliers are offering additional ways to help clients via cyber warranties – reflecting more sophisticated and capable products and services. For executives who continue to grapple with the rapid changes, read on to understand the cyber insurance parameters you should consider and the role that robust IT solutions play.

Cyber Insurance Requirements & Considerations
Depending on your organization's coverage needs, you may find a request for many of the items below within a cyber insurance policy document. Keep this list handy when applying for or renewing cyber insurance, and feel free to reach out to our team if you need help understanding any of them. These are the areas that your managed service provider should be guiding you on to ensure they are in place.
- Enforcement of identity and access management
- Increased requirement for email security screening
- Identified and segregated unsupported and end-of-life (EOL) software
- Limited domain administrator accounts within an organization's network
- Implemented security products and solutions to prevent and detect malicious network activity
- Applied baseline standards and vulnerability scans for devices with network connections
- Dedicated backup and recovery processes with data recovery point objectives (RPO) and recovery time objectives (RTO)
- Directed tabletop exercises to test and inform an incident response plan
Enforcement of identity and access management
Extend MultiFactor Authentication (MFA) to all users who have access to your network. This includes volunteers or third-party contractors -- anyone with an account on your network. This is a baseline requirement and increasingly difficult with remote work arrangements.
SE Guidance
Enabling MFA is not a new recommendation; it has been at the top of the cybersecurity best practices list for years. The issue resides in an organization's slow pace and lack of commitment to implementing MFA. If you have not deployed MFA throughout your company, you are inviting unnecessary risk. Cyber insurers now have MFA as a mandate. Put this low-cost, highly effective cloud security defense measure in place today.
Increased requirement for email security screening
Email is the easiest way into a network for cybercriminals. There are systemic controls that can be put in place, but end-users play a major role in keeping this inroad secure. Security controls for emails must include:
-
screening and quarantining for malicious links and attachments
-
tagging
-
detonation
-
evaluation of attachments in a sandbox
-
new/updated policy and reporting standards
-
testing and training for phishing email simulations should be conducted at least every six months so all users can identify fraudulent or spoofed emails.
SE Guidance
Phishing and ransomware attacks are proliferating and becoming more sophisticated every day. With the advent of generative AI capabilities in the hands of hackers, it is easier than ever for attacks to be more personalized and more successful. Cybercriminals are constantly adapting tactics to trick spam filters and fool unsuspecting victims to gain access to your organization's sensitive information. You can get in front of these hacker attempts by creating a culture of security through security awareness training for all users – executives to interns – and implementing the right email security measures. This is an area where your MSP needs to be ultra-sophisticated, utilizing the latest training, best practices, and technologies.
Identified and segregated unsupported and end-of-life (EOL) software
This is perhaps one of the most challenging and frustrating aspects of cybersecurity for IT administrators. You need the ability to discover and map devices or endpoints connected to your network to help maintain an up-to-date configuration management database (CMDB). Any EOL and end-of-support (EOS) software or products should be segregated from your network and supplementally supported.
Guidance
EOL/EOS software does not receive maintenance or patches, leaving this legacy tech open to vulnerabilities. EOL management is now a prerequisite for cyber insurance. Running EOL or EOS software leaves the network they are connected to vulnerable to attacks by essentially creating unsecured and unmonitored backdoors into your network, which cybercriminals waste no time exploiting. Running regular audits and adding inquiries into software accounts as part of the exit interview process are two ways to manage this.
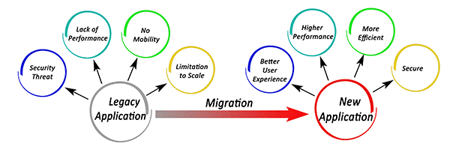
When planning for outdated technology, time must be accounted for in each process phase: from analyzing options, making decisions, lead times for engineering talent and hardware, to training employees for ‘go-live.' A solid EOL management strategy and an asset inventory maintenance program will help you control risk, reduce unforeseen budget expenses, and better plan for supply chain issues that cause delays.
|
Check here for a list of upcoming EOL/EOS dates for widely used products. EOL upgrades are critical to your network's security, functionality, and performance. Your managed service provider should be proactively managing EOL through annual budgeting and planning. |
Limited domain administrator accounts within an organization's network
As part of data breach prevention, the "least privilege" principle should be applied to administrator or service accounts that, by default, have the most access and control within your organization's network. Along with limiting access, these service accounts must be uniquely monitored for unusual activity and password management.
SE Guidance
Organizations need to expand data breach prevention and network protection to include people, devices, apps, and data found in remote work environments to a 'Zero Trust' environment. With Zero Trust, your network no longer implicitly trusts anyone or anything, inside or outside your network boundary. Each access request must be fully authenticated, authorized, and encrypted before access is granted. Using the idea of 'least privilege,' just-in-time and just-enough-access (JIT/JEA) principles are applied to minimize lateral movement within your network (access to one network resource does not grant automatic access to another). It’s surprising just how often key privileges are not managed correctly.
Implemented security products and solutions to prevent and detect malicious network activity
Endpoint protection and response solutions dedicated to network protection, designed to detect known threats, as well as changes in the operation and behavior of endpoints, are a standard requirement. These are next-generation virus scanning tools, such as endpoint detection & response (EDR), combined with a centralized team dedicated to monitoring and remediating identified security threats, known as a security operations center (SOC).
SE Guidance
The need for greater visibility and depth of response to cyberthreats across your entire digital landscape is not just a cybersecurity best practice; it's a requirement to obtain cyber insurance. You may have some form of network security monitoring in place; however, many organizations must have advanced network monitoring. This new model combines security operations expertise, threat intelligence at endpoints, networks, identity, and cloud resources, along with 24x7 monitoring capabilities. This level of response is key to securing your organization against the increasing dangers of advanced cyberattacks.
Applied baseline standards and vulnerability scans for devices with network connections
You may hear the term 'harden' in relation to systems and devices connecting to your network. This means you need to have a set of standards and tools in place that will secure any new endpoints or systems introduced to the network, including MFA enforcement, patching updates, device monitoring, etc. It is also a best practice to conduct penetration testing of the network and vulnerability scanning of devices on that network at least annually.
SE Guidance
It may be easy to assume that patching is less critical now that more data lives in replicated cloud storage environments, but it is actually the opposite. Our “work-from-anywhere” society, access to multiple network environments, and increasing occurrences of cyberattacks make it more important than ever to approach patching and software updates with urgency and completeness in mind. By implementing a solid patch management process and system parameters for network access within your organization, you can harden your security posture and become less attractive to cybercriminals. Your managed services provider must have a clear and documented process to proactively address patching and updates.
Dedicated backup & recovery processes with data recovery point objectives (RPO) & recovery time objectives (RTO)
Every business should have a data backup and recovery strategy. This strategy should include protecting data in backup systems from compromise. Before a ransomware breach, you must predetermine how long your organization can be down (RTO) and how much data can be lost (RPO) before it can be functional again. In other words, what is an acceptable loss? If implemented correctly, this mitigates the effects of ransomware attacks.
SE Guidance
Data loss affects all organizations at some point, and the type of industry you are in can dictate certain requirements of your backup and recovery strategy. Knowing your RTO and RPO will help determine the type of backup and recovery process you need. Do you have a tape-based, air-gapped backup system that needs to be augmented with a cloud backup service or vice-versa? Each determination will have a dollar figure associated, so the right combination is paramount to optimizing costs.
 Develop a robust Incident Response Plan and test it annually.
Develop a robust Incident Response Plan and test it annually.
If your business is hit with ransomware or another cyberattack, you need to know (and be able to show) how your organization will respond. An Incident Response Plan (IRP) outlines your response strategy to a cybersecurity incident. This plan should be regularly updated and tested. Testing should involve incident response team members for awareness and input. Regular testing is especially important given the frequency of network changes and IT staff turnover rates businesses are currently experiencing.
SE Guidance
Testing your IRP is the best way to ascertain reliability. Regular incident response tabletop exercises are a best practice. With executives now being held accountable for cyber breaches, it is important to get involved to fully understand the cybersecurity controls and preventative measures you have in place.
Are you covered?
Domestic cyberattacks on large and small companies motivated a national awareness for increased cybersecurity, which prompted an increase in industry regulations. Cybersecurity requirements are no longer limited to companies with high compliance and regulation obligations. Getting and maintaining cyber insurance is now a must for all businesses, regardless of industry or size. That's why understanding your organization's cyber risks and insuring against them is an executive business-level initiative. To stay ahead of the requirements, we suggest alignment of company operations around our aCSF (Adaptive Cybersecurity Framework), which includes many aspects of NIST.
As your managed IT and security services partner, Systems Engineering will effectively support your technology and end-users and improve your cyber defense posture. By staying on top of trends and the industry shifts influencing tech spending and regulations, we can help you make sound investments that enhance productivity, harden your cyber defenses, and improve your cyber resilience.
We're working with our clients on their 2024 technology strategies and initiatives, ensuring that they are assessing and covering their cyber risks appropriately. Updating an organization's cyber maturity journey is both art and science: our approach includes the Systems Engineering aCSF (Adaptive Cybersecurity Framework), which allows for flexibility as it aligns actions and outcomes with the NIST Cybersecurity Framework and reflects best practices gained from our more than 35 years of experience. The Systems Engineering Adaptive Cybersecurity Framework (aCSF) takes into account all of the above initiatives, providing a standardized and, scalable approach that satisfies many cyber insurance requirements. The result is a demonstrable strategy that enables our clients to clearly articulate their cybersecurity posture when applying for or renewing cyber insurance coverage.
If you recognize potential gaps in your current IT operation or would like to discuss any of the cybersecurity solutions recommended in this article, contact us at info@systemsengineering.com or call 888.624.6737 to speak to a Systems Engineering representative.