Proactively defending against cyberattacks and incidents within your organization is the main goal of any good cybersecurity strategy. But what happens WHEN, not IF, your company experiences a cyber incident? The 2023 Data Breach Investigations Report by Verizon1 highlights the escalating threat of cybercriminals targeting organizations for data. With evolving attack methods and 95% of breaches financially driven, prioritizing cybersecurity measures and rapid breach detection is critical for effective protection and recovery.
It is not enough to focus efforts on defensive cyber protection. Proper attention must also be given to business recovery and continuation in the event of a cyber incident. The National Institute of Standards and Technology (NIST) defines a cyber-resilient organization2 as one that has done as much as possible to anticipate and withstand a cyberattack and... has planned as much as possible to quickly recover, adapt, and resume operations that depend on cyber resources following a cyber incident.

Cyber Resilience
If you are aligned with NIST, cyber resilience goes beyond recovery after an event. A cyber-resilient strategy also includes the ability to limit the effects of a security incident while delivering services despite any failures resulting from an attack. Continuous service delivery involves restoring existing service methods, as well as the ability to modify service methods to adapt to evolving cyber risks and maintain secure business.
The question is, how can your business become cyber-resilient? At the core of an effective cybersecurity strategy, you must have well-developed security policies and plans. These plans will outline how your company protects itself and its technology assets. Following are the basic components to get you started down the path to proactively position your company to be cyber resilient.
Define & Measure Cyber Risk
Risks are constantly evolving, so a key element of cyber resilience is to have a clear understanding of risk and define an acceptable level within your organization. Measuring your risk profile should be a recurring exercise – typically every 6-12 months - so you can focus resources on the cyber risks with the greatest potential impact as threats evolve. What was a major cyber risk a year ago may now be mitigated, and a new attack surface with a new risk has developed in its place.
Manage & Mitigate Cyber Risk
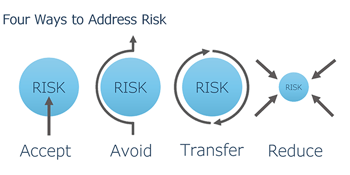
Once cyber risks have been identified and evaluated, it’s necessary to implement best practices to reduce the likelihood and limit the effects of an attack. By expanding the focus beyond simply preventing criminal network entry, you begin to address cyber resilience strategies like data deletion policies, proper backup and recovery processes, continuing operations during a disruptive cyber event, and any number of strategies that focus on limiting the effects of an attack and the ability to recover with limited damages.
“What is risk? Risk is uncertainty about the outcome. The less data you have, the more uncertainty you have about the outcome.”
– David Friedberg
Review & Challenge Business Continuity Plans
One of the most important documents your organization can create is a Business Continuity Plan (BCP). This plan comprehensively reviews how your organization can preserve business continuity when responding to cyber incidents that cause business disruption of critical operational processes, applications, and IT infrastructure.
With persistent and increasingly sophisticated cyber threats, the complexity of securing hybrid workforces, poor cybersecurity habits, extensive ecosystems, and the ongoing threat of cyber warfare, BCPs need to be reviewed and challenged annually. Review existing use cases and develop new ones that reflect changes to your business operations. Capture opportunities for improvement, and communicate (at a high level) to all stakeholders what their roles and responsibilities are in the case of a cyber attack. This could include external communication in the case of a data breach that affects customer data. Your Board of Directors should also be given a copy of the Business Continuity Plan.
Test Backup & Recovery Plans

It's not enough to have a data backup solution in place and check a box. You must have an ongoing strategy that evaluates your data and applications to determine how long you can afford to be down (Recovery Time Objective-RTO), and how much data you can afford to lose (Recovery Point Objective-RPO) as well as replication alternatives. Because data loss can happen at any time, even without a cyber incident, the RTO and RPO both need to be carefully considered and tested as both have financial implications. With proper planning, a data recovery effort can be taken from days, to hours, directly impacting the resilience of your company.
Create a Culture of Security
A cyber-resilient organization is highly dependent upon the company leadership's priority and attitude toward cyber risk. Business leaders will influence the culture of security, which is built on policies and procedures that are enforced throughout the company. Some of the usual policies related to cybersecurity include the following:
- INFORMATION SECURITY POLICY: Define the standards and processes your company uses to secure your network and data from internal and external risks, including new technologies like AI.
- TECHNOLOGY ACCEPTABLE USE AGREEMENT: Articulate acceptable employee uses of your company's technology, in addition to the consequences of misuse.
- BUSINESS CONTINUITY PLAN: Demonstrate to your clients, shareholders, and partners that your business is prepared for the worst.
- SECURITY AWARENESS TRAINING: Formal and ongoing security training for employees that reinforces proper end-user behavior through simulated phishing attacks.
Moving forward with an understanding that no organization can be 100% protected from a cyberattack, our current threat landscape makes it rational to assume a disruption will eventually occur. With this in mind, ensure preparations are in place to respond to and recover from a cyber incident with as limited impact on operations, the financial bottom line, and your organization's reputation as possible.
Being prepared and building cyber-resilience means keeping your organization secure within a landscape of constantly evolving threats while maintaining productivity during and after an event.
1. https://www.verizon.com/business/resources/infographics/2023-dbir-infographic.pdf
2. https://csrc.nist.gov/glossary/term/cyber_resiliency
For more information on improving your organization's cyber resiliency, connect with us at info@systemsengineering.com or call 888.624.6737. Clients, please get in touch with your Systems Engineering Account Manager.